ServiceNow SecOps connector and actionedit
The ServiceNow SecOps connector uses the import set API to create ServiceNow security incidents. You can use the connector for rule actions and cases.
Prerequisitesedit
After upgrading from Elastic Stack version 7.15.0 or earlier to version 7.16.0 or later, you must complete the following within your ServiceNow instance before creating a new ServiceNow SecOps connector or updating an existing one:
- Install Elastic for Security Operations (SecOps) from the ServiceNow Store.
- Create a ServiceNow integration user and assign it the appropriate roles.
- Create a Cross-Origin Resource Sharing (CORS) rule.
-
If you use open authorization (OAuth), you must also:
Create a ServiceNow integration useredit
To ensure authenticated communication between Elastic and ServiceNow, create a ServiceNow integration user and assign it the appropriate roles.
- In your ServiceNow instance, go to System Security → Users and Groups → Users.
- Click New.
- Complete the form, then right-click on the menu bar and click Save.
- Go to the Roles tab and click Edit.
-
Assign the integration user the following roles:
-
import_set_loader -
import_transformer -
personalize_choices -
sn_si.basic -
x_elas2_sir_int.integration_user
-
- Click Save.
Create a CORS ruleedit
A CORS rule is required for communication between Elastic and ServiceNow. To create a CORS rule:
- In your ServiceNow instance, go to System Web Services → REST → CORS Rules.
- Click New.
-
Configure the rule as follows:
- Name: Name the rule.
-
REST API: Set the rule to use the Elastic SecOps API by choosing
Elastic SIR API [x_elas2_sir_int/elastic_api]. - Domain: Enter the Kibana URL, including the port number.
- Go to the HTTP methods tab and select GET.
- Click Submit to create the rule.
Create an RSA keypair and add an X.509 Certificateedit
This step is required to use OAuth for authentication between Elastic and ServiceNow.
Create an RSA keypair:
Add an X.509 certificate to ServiceNow:
- In your ServiceNow instance, go to Certificates and select New.
-
Configure the certificate as follows:
- Name: Name the certificate.
- PEM Certificate: Copy the generated public key into this text field.
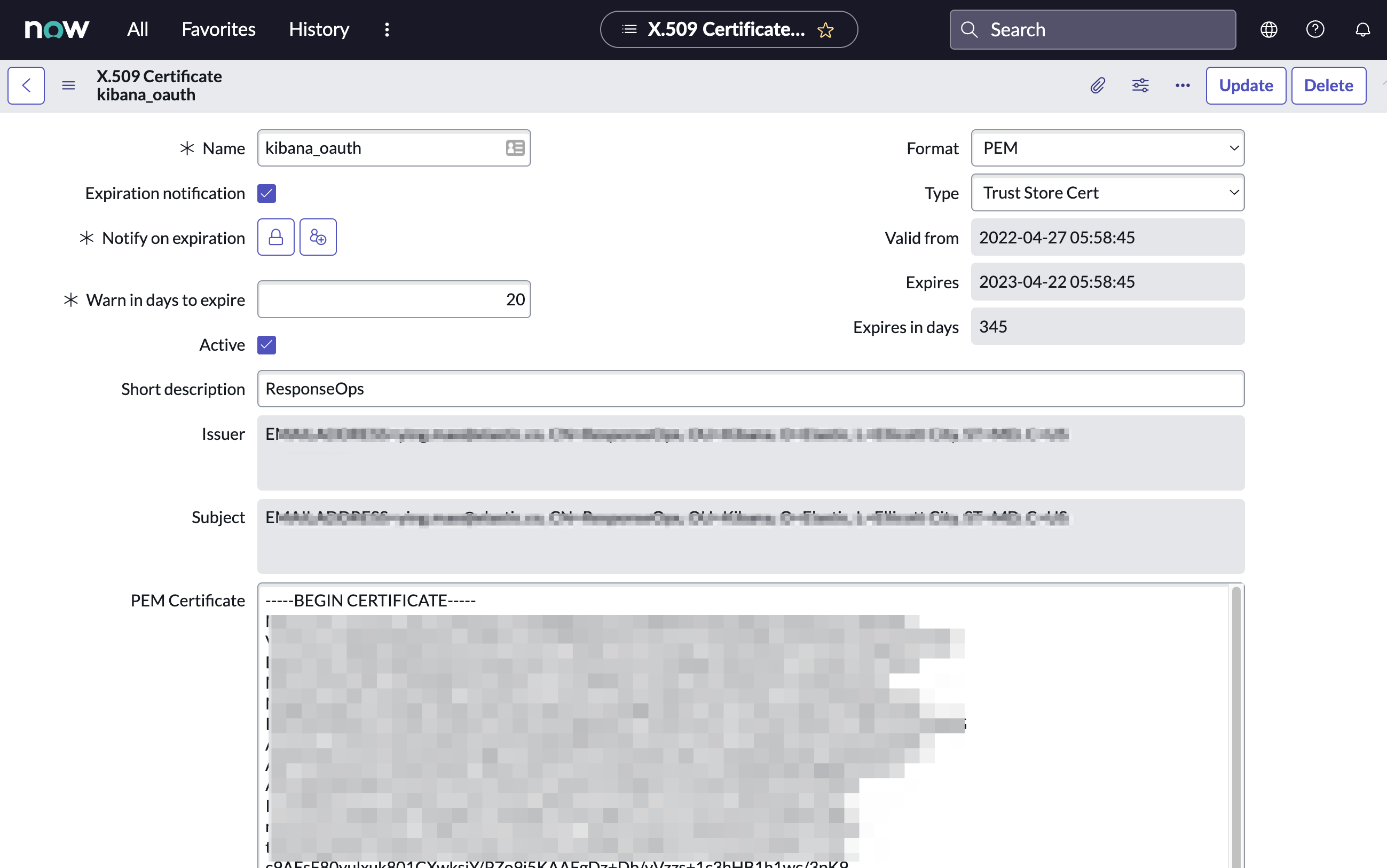
- Click Submit to create the certificate.
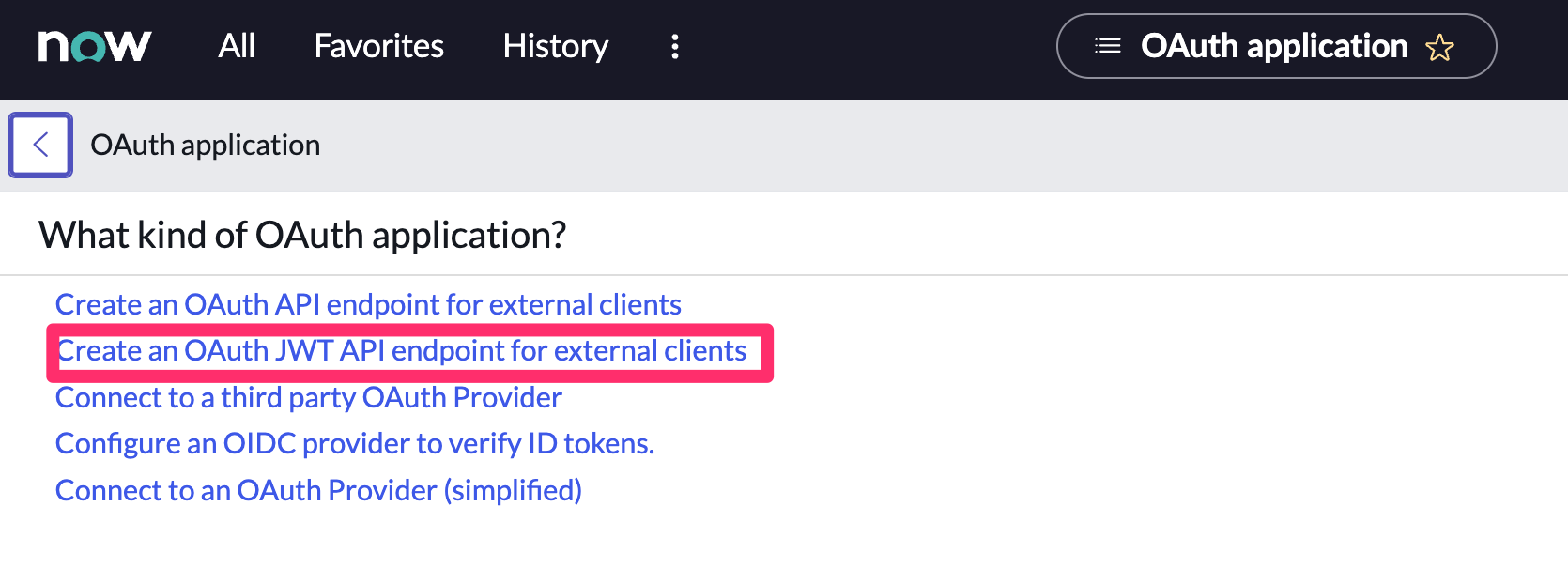
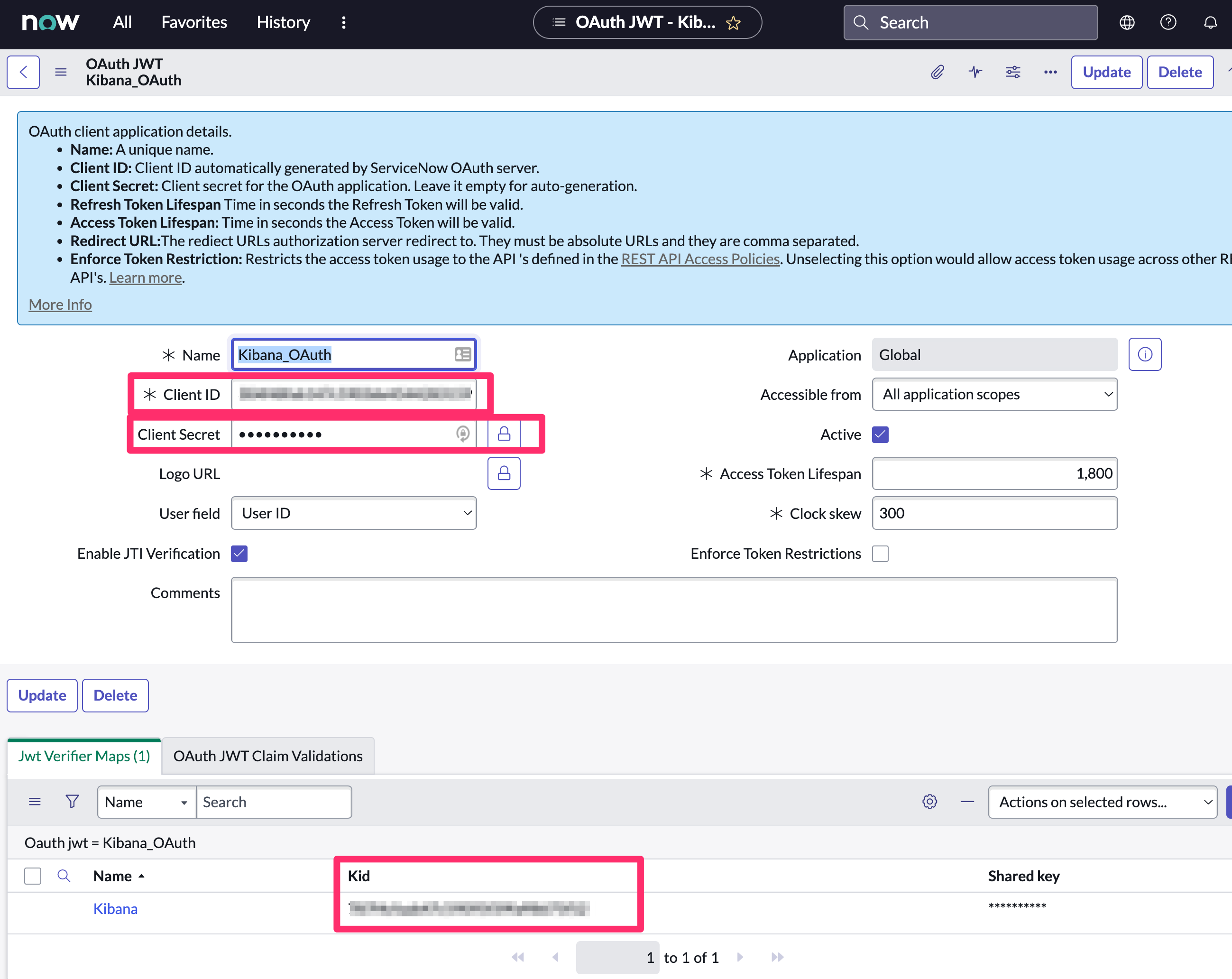
Create an OAuth JWT API endpoint for external clients with a JWT Verifiers Mapedit
This step is required to use OAuth for authentication between Elastic and ServiceNow.
- In your ServiceNow instance, go to Application Registry and select New.
-
Select Create an OAuth JWT API endpoint for external clients from the list of options.
-
Configure the application as follows:
- Name: Name the application.
- User field: Select the field to use as the user identifier.
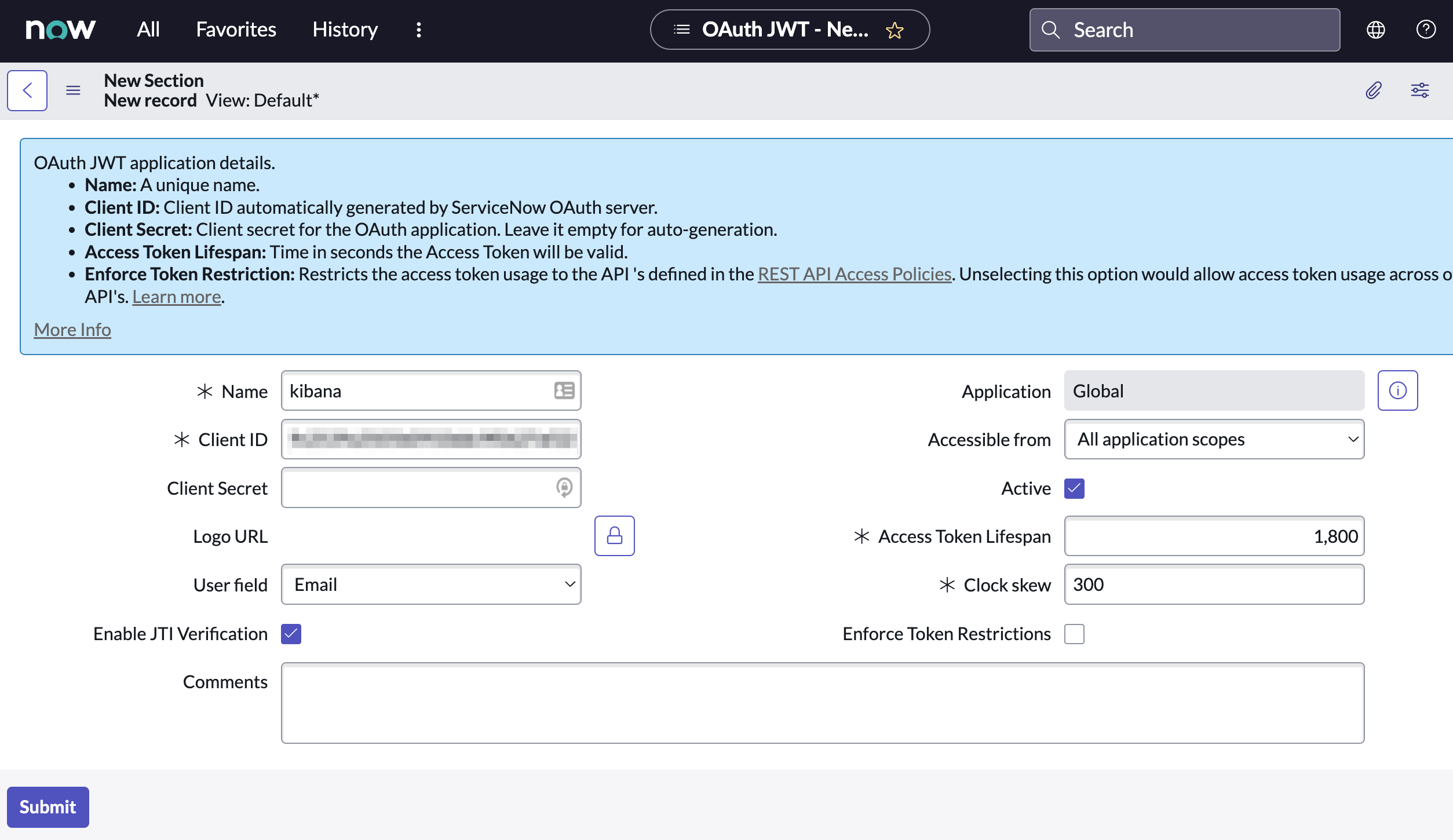
Remember the selected user field. You will use this as the User Identifier Value when creating the connector. For example, if you selected Email for User field, you will use the user’s email for the User Identifier Value.
- Click Submit to create the application. You will be redirected to the list of applications.
- Select the application you just created.
- Find the Jwt Verifier Maps tab and click New.
-
Configure the new record as follows:
- Name: Name the JWT Verifier Map.
- Sys certificate: Click the search icon and select the name of the certificate created in the previous step.
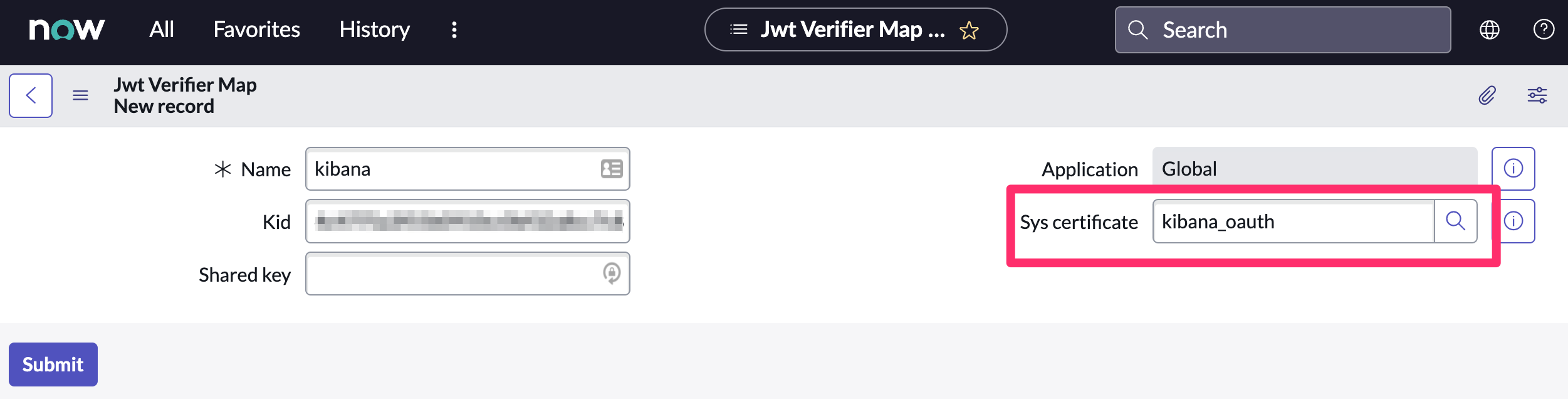
- Click Submit to create the verifier map.
-
Note the Client ID, Client Secret and JWT Key ID. You will need these values to create your ServiceNow connector.
Update a deprecated ServiceNow SecOps connectoredit
ServiceNow SecOps connectors created in Elastic Stack version 7.15.0 or earlier are marked as deprecated after you upgrade to version 7.16.0 or later. Deprecated connectors have a yellow icon after their name and display a warning message when selected.
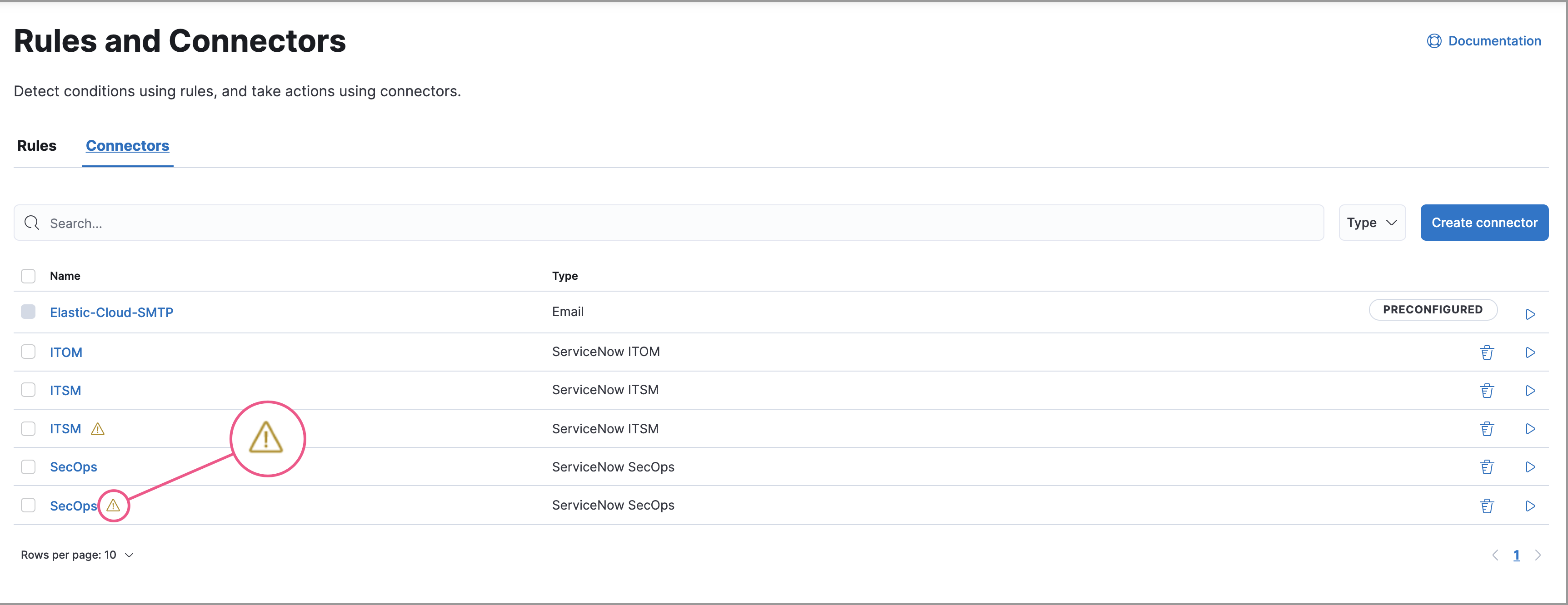
Deprecated connectors will continue to function with the rules they were added to and can be assigned to new rules. However, it is strongly recommended to update deprecated connectors or create new ones to ensure you have access to connector enhancements, such as updating incidents.
To update a deprecated connector:
- Open the main menu and go to Stack Management > Connectors.
- Select the deprecated connector to open the Edit connector flyout.
- In the warning message, click Update this connector.
-
Complete the guided steps in the Edit connector flyout.
- Install Elastic for Security Operations (SecOps) from the ServiceNow Store and complete the required prerequisites.
- Enter the URL of your ServiceNow instance.
- Enter the username and password of your ServiceNow instance.
- Click Update.
Create connectors in Kibanaedit
You can create connectors in Stack Management > Connectors or as needed when you’re creating a rule. You must choose whether to use OAuth for authentication.
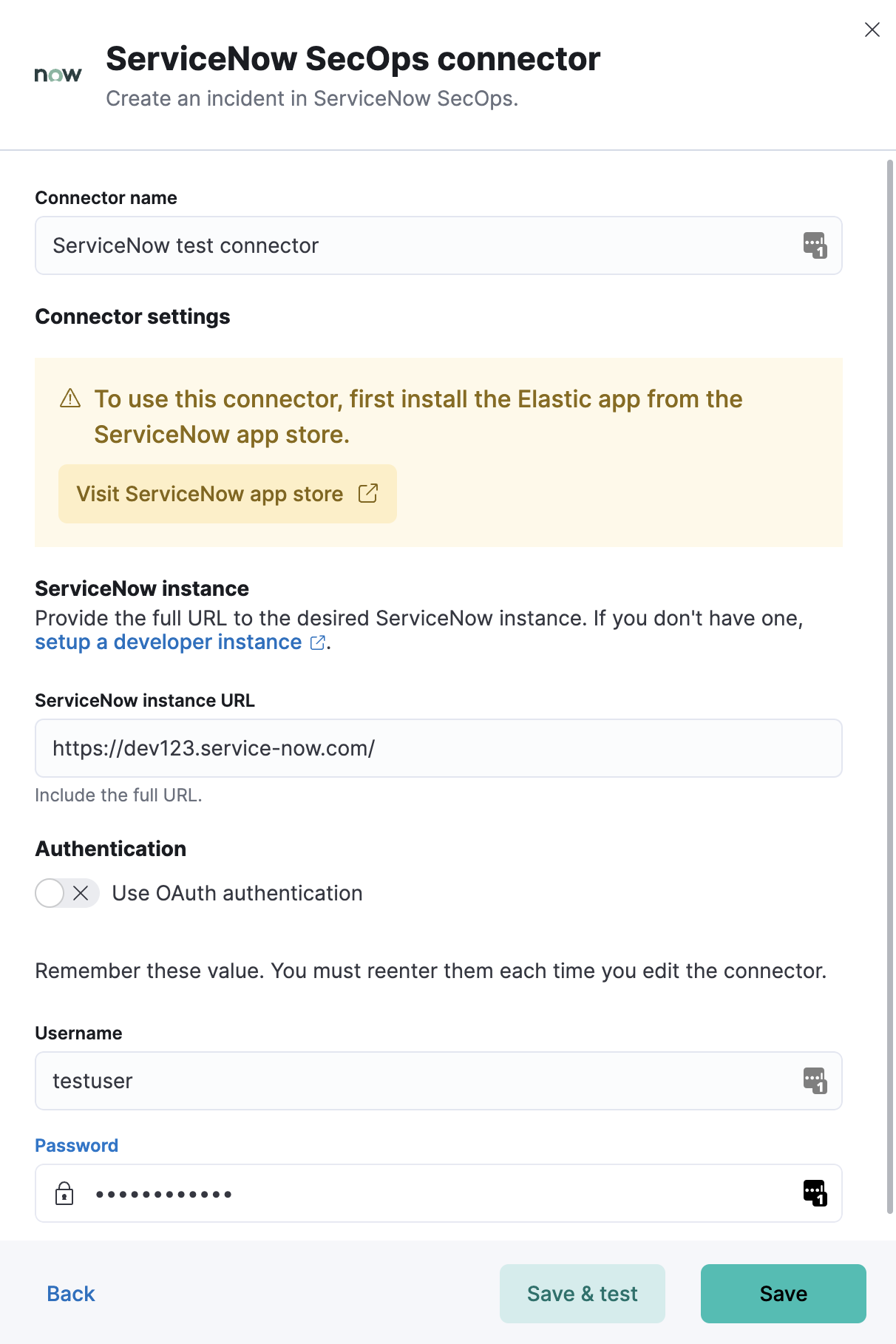
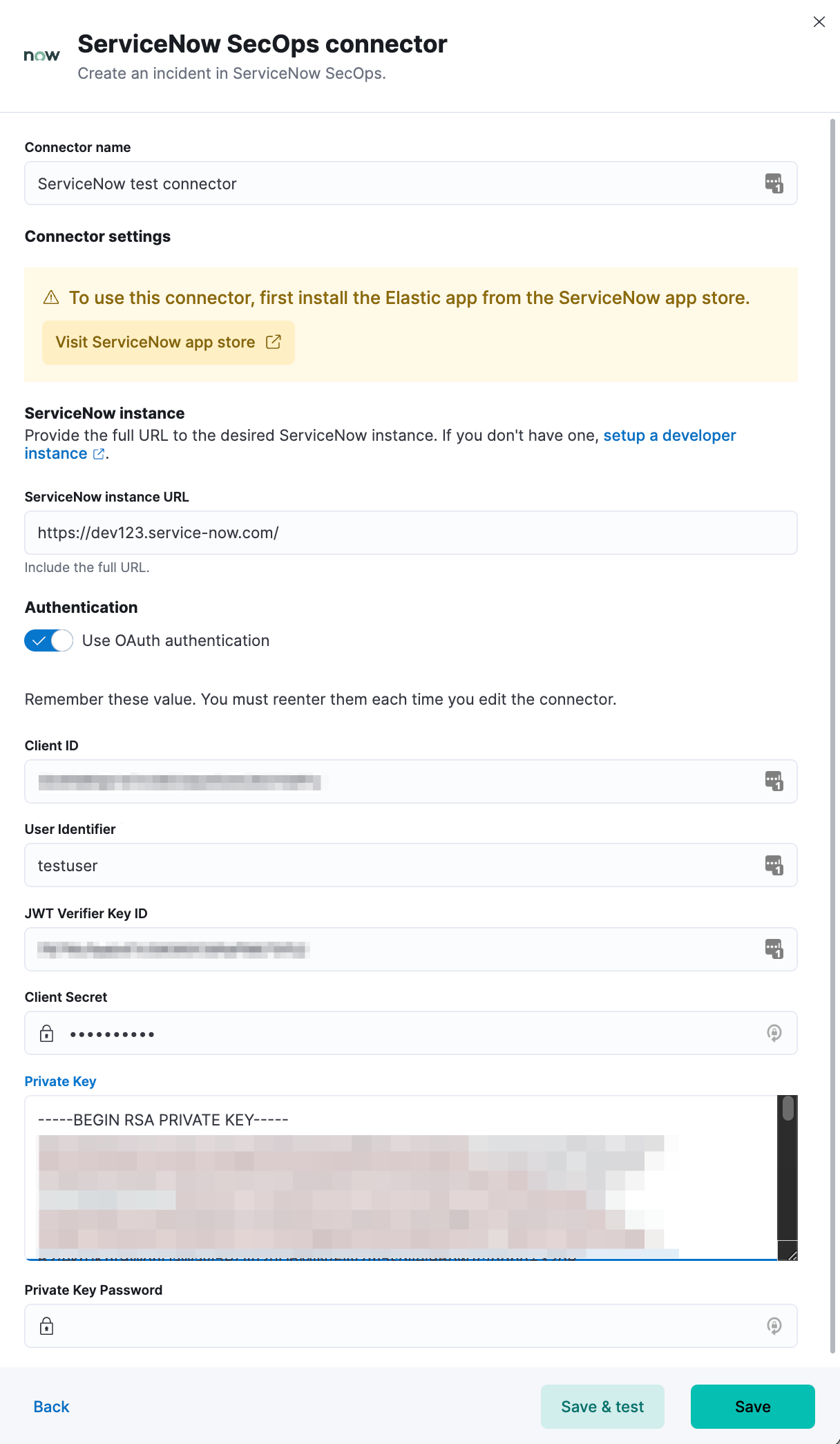
Connector configurationedit
ServiceNow SecOps connectors have the following configuration properties:
- Name
- The name of the connector.
- Is OAuth
- The type of authentication to use.
- URL
- ServiceNow instance URL.
- Username
- Username for HTTP Basic authentication.
- Password
- Password for HTTP Basic authentication.
- User Identifier
- Identifier to use for OAuth type authentication. This identifier should be the User field you selected during setup. For example, if the selected User field is Email, the user identifier should be the user’s email address.
- Client ID
- The client ID assigned to your OAuth application.
- Client Secret
- The client secret assigned to your OAuth application.
- JWT Key ID
- The key ID assigned to the JWT verifier map of your OAuth application.
- Private Key
- The RSA private key generated during setup.
- Private Key Password
- The password for the RSA private key generated during setup, if set.
Create preconfigured connectorsedit
If you are running Kibana on-prem, you can define connectors by
adding xpack.actions.preconfigured settings to your kibana.yml file.
For example:
Connector using Basic Authentication
xpack.actions.preconfigured:
my-servicenow-sir:
name: preconfigured-servicenow-connector-type
actionTypeId: .servicenow-sir
config:
apiUrl: https://example.service-now.com/
usesTableApi: false
secrets:
username: testuser
password: passwordkeystorevalue
Connector using OAuth
xpack.actions.preconfigured:
my-servicenow:
name: preconfigured-oauth-servicenow-connector-type
actionTypeId: .servicenow-sir
config:
apiUrl: https://example.service-now.com/
usesTableApi: false
isOAuth: true
userIdentifierValue: testuser@email.com
clientId: abcdefghijklmnopqrstuvwxyzabcdef
jwtKeyId: fedcbazyxwvutsrqponmlkjihgfedcba
secrets:
clientSecret: secretsecret
privateKey: -----BEGIN RSA PRIVATE KEY-----\nprivatekeyhere\n-----END RSA PRIVATE KEY-----
Config defines information for the connector type.
-
apiUrl - An address that corresponds to URL.
-
usesTableApi - A boolean that indicates if the connector uses the Table API or the Import Set API.
If usesTableApi is set to false, the Elastic application should be installed in ServiceNow.
-
isOAuth - A boolean that corresponds to Is OAuth and indicates if the connector uses Basic Authentication or OAuth.
-
userIdentifierValue -
A string that corresponds to User Identifier. Required if
isOAuthis set totrue. -
clientId -
A string that corresponds to Client ID, used for OAuth authentication. Required if
isOAuthis set totrue. -
jwtKeyId -
A string that corresponds to JWT Key ID, used for OAuth authentication. Required if
isOAuthis set totrue.
Secrets defines sensitive information for the connector type.
-
username -
A string that corresponds to Username. Required if
isOAuthis set tofalse. -
password -
A string that corresponds to Password. Should be stored in the Kibana keystore. Required if
isOAuthis set tofalse. -
clientSecret -
A string that corresponds to Client Secret. Required if
isOAuthis set totrue. -
privateKey -
A string that corresponds to Private Key. Required if
isOAuthis set totrue. -
privateKeyPassword - A string that corresponds to Private Key Password.
Test connectorsedit
You can test connectors with the run connector API or as you’re creating or editing the connector in Kibana. For example:
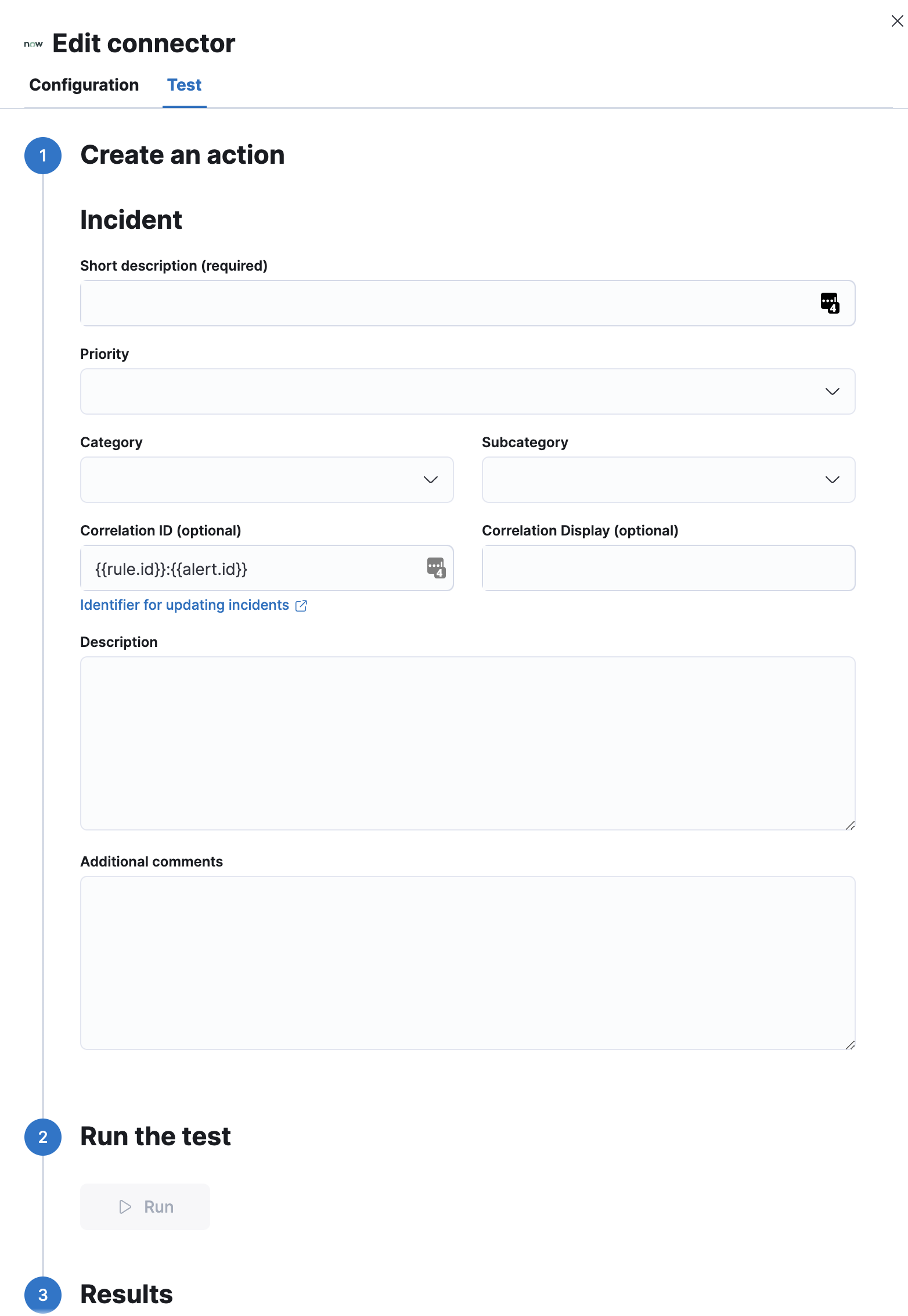
ServiceNow SecOps actions have the following configuration properties.
- Short description
- A short description for the incident, used for searching the contents of the knowledge base.
- Priority
- The priority of the incident.
- Category
- The category of the incident.
- Subcategory
- The subcategory of the incident.
- Correlation ID
-
Connectors using the same Correlation ID will be associated with the same ServiceNow incident. This value determines whether a new ServiceNow incident will be created or an existing one is updated. Modifying this value is optional; if not modified, the rule ID and alert ID are combined as
{{ruleID}}:{{alert ID}}to form the Correlation ID value in ServiceNow. The maximum character length for this value is 100 characters.
Using the default configuration of {{ruleID}}:{{alert ID}} ensures that ServiceNow will create a separate incident record for every generated alert that uses a unique alert ID. If the rule generates multiple alerts that use the same alert IDs, ServiceNow creates and continually updates a single incident record for the alert.
- Correlation Display
- A descriptive label of the alert for correlation purposes in ServiceNow.
- Description
- The details about the incident.
- Additional comments
- Additional information for the client, such as how to troubleshoot the issue.
Connector networking configurationedit
Use the Action configuration settings to customize connector networking configurations, such as proxies, certificates, or TLS settings. You can set configurations that apply to all your connectors or use xpack.actions.customHostSettings to set per-host configurations.
Configure ServiceNow SecOpsedit
ServiceNow offers free Personal Developer Instances, which you can use to test incidents.